

At its core, a Penetration Test assesses perceived technical control vs actual control. This means that if you build a system, application or infrastructure, it will have inherent weaknesses. These weaknesses are mitigated through design decisions, technology choices and architectural approaches. The Penetration Test seeks to validate whether or not those decisions, choices and approaches worked.
To that end, there are many types of tests that could be suitable to your project or situation, some of which are detailed below:
Infrastructure is fundamental to an organisation’s daily operations, encompassing everything from the full enterprise network to specific critical systems. If a malicious actor were to breach this network, the implications could be extensive and potentially grant them complete access to crucial internal resources. In extreme cases, they might even halt operations, as seen in ransomware attacks.
Web applications are used more frequently to service needs for business operations, product marketing, and promotion. These platforms often handle payment processing and the management of Personally Identifiable Information (PII) and other sensitive data. If such systems are breached, the consequences could range from reputational harm and regulatory penalties to even more severe outcomes.
Cloud computing has emerged as an appealing solution for businesses of all sizes, from nimble startups to expansive corporations, with cost-effectiveness and enhanced security standing out as the primary incentives. Cloud security testing is vital to maintaining the integrity and security of a company’s cloud-based resources.
An Application Programming Interface (API) is the nerve centre for numerous applications, facilitating efficient data access and exchange. With their ability to employ application logic and retain sensitive data like Personally Identifiable Information (PII), APIs have increasingly become a focal point for cyberattacks.
Mobile application testing is essential for performance, security and compliance. It helps to ensure a high-quality, secure, and user-friendly app.
Wireless networks are used throughout most organisations to allow employees access to the internet, company networks and applications. They are commonly offered to guests and visitors to a business. However, given the inherent nature of wireless networks, which can often be accessed beyond the physical confines of the business premises, particularly in shared office spaces, they can pose substantial security risks if not configured with due care and diligence.
Social engineering encompasses a wide spectrum of malevolent actions achieved via human interaction. Despite having the most stringent technological safeguards, employees could inadvertently become conduits for these attacks if they are not adequately trained and tested to identify such incidents.
Testing of Electric Vehicle (EV) charging stations is crucial in safeguarding these components of our growing green infrastructure. It aims to identify software vulnerabilities which, if exploited, could disrupt charging services and potentially lead to the misuse of sensitive user data such as payment details. It fortifies these systems against cyber threats and demonstrates a commitment to security, instilling trust among users.
“Red Team” or “Tiger Team” testing takes a standard Penetration Test further by including multiple areas of focus driven by specific threat assessment data about your organisation. Typically, these engagements are much larger and include phases for Open-Source Intelligence (OSINT) gathering and specific client targeting. In addition, the use of physical, social engineering techniques over and above technical ones such as phishing, are used to gain access to unsecured locations within the organisation. The goal of red/tiger teaming is to simulate a real-world attack by a well-motivated and well-funded attacker.
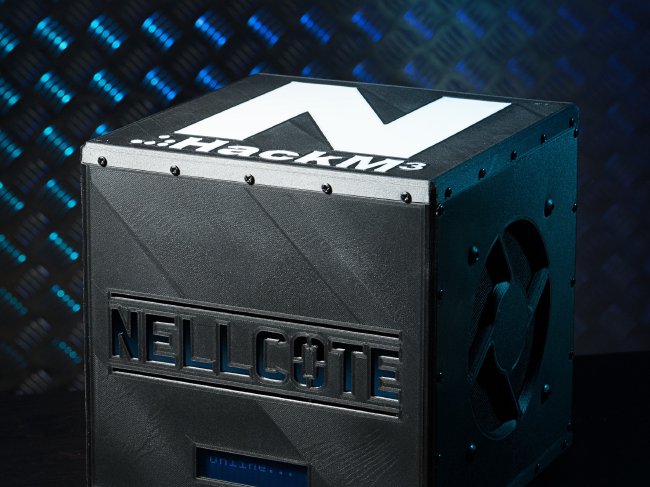
The Nellcote Hackme3 assessment is a targeted attack simulation designed to establish what, if any, low hanging fruit exists within the IT infrastructure and what could be leveraged to gain a foothold in the estate or full network access.
In the era of digital transformation, businesses are increasingly adopting cloud services to optimize performance, flexibility, and scalability. At Nellcote, we specialise in Cloud Testing and Optimisation for Office 365, Azure, and AWS, helping organizations ensure their cloud systems are both robust and efficient.
Whether you’re planning a transition to the cloud or aiming to optimise your existing infrastructure, our team of experienced and certified professionals is equipped to support you. Our services include:
Our methodology consists of several stages to provide comprehensive testing and optimisation:
At Nellcote, we believe in delivering cloud services that not only meet but exceed your expectations. Trust us to ensure your O365, Azure, and AWS services are secure, efficient, and tailored to your unique business requirements. Contact us to discover how we can help optimise your cloud journey.
Responding to incidents in Realtime is difficult and fraught with issues. Our real-world cyber crisis simulations bring breaches to life and let you play them out in a safe, yet immersive way.
These are designed to be as realistic as possible with several prebuilt scenarios to choose from -Including real-time inputs, changes in the game and media injects.
The injects are designed to keep you on your toes and prepare you for the inevitable. Our simulations are ideal for board members and leadership teams and will often lead to the identification of gaps within the current process that could lead to inefficient incident management.
A code review involves an in-depth analysis of the source code of an application or software system. The goal is to identify security vulnerabilities, coding flaws, and weaknesses that could potentially be exploited by attackers.
Our key steps:
